Risk Management Enterprise for Beginners
Wiki Article
The Single Strategy To Use For Risk Management Enterprise
Table of ContentsRisk Management Enterprise - The Facts7 Simple Techniques For Risk Management EnterpriseThe Ultimate Guide To Risk Management EnterpriseThe smart Trick of Risk Management Enterprise That Nobody is Talking AboutThe Best Guide To Risk Management Enterprise7 Easy Facts About Risk Management Enterprise ExplainedRisk Management Enterprise - The Facts
Real-Time Risk Evaluations and Mitigation in this software application allow organizations to constantly keep an eye on and examine dangers as they advance. Once risks are identified, the software helps with immediate reduction activities.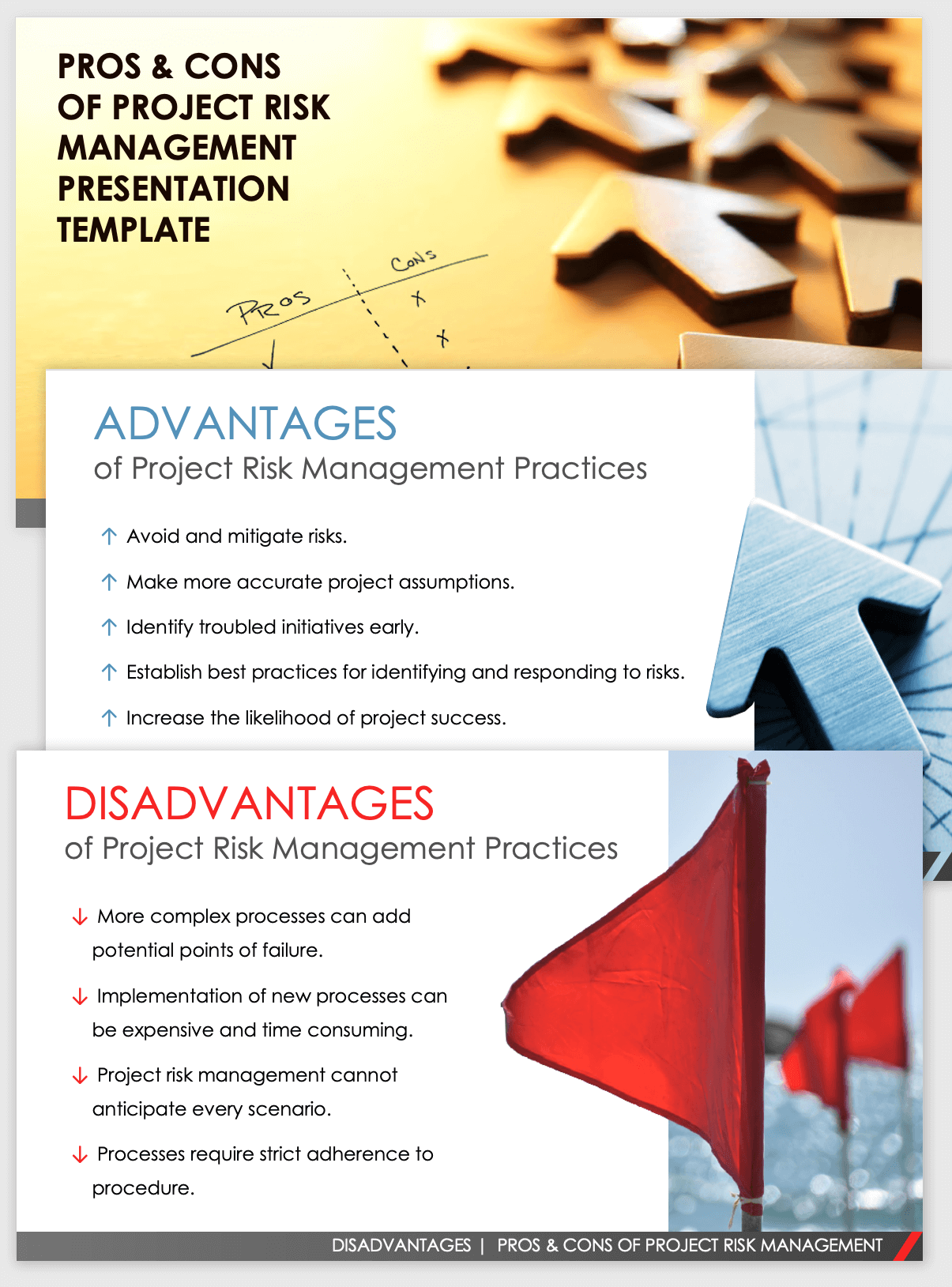
KRIs fix the problem of irregular or uncertain danger assessment. They attend to the difficulty of continuous danger monitoring by offering tools to keep an eye on risks continually. KRIs boost safety threat oversight, making sure that potential dangers are determined and managed efficiently. The job of threat administration must not be a challenge. Companies must depend on a superior and innovative threat management software program.
Risk Management Enterprise Things To Know Before You Get This
IT run the risk of management is a subset of business threat monitoring (ERM), designed to bring IT take the chance of in accordance with an organization's threat appetite. IT take the chance of monitoring (ITRM) encompasses the plans, procedures and innovation necessary to minimize risks and vulnerabilities, while preserving conformity with applicable regulative needs. On top of that, ITRM seeks to restrict the consequences of destructive occasions, such as safety violations.While ITRM structures provide helpful support, it's very easy for IT teams to deal with "framework overload." Veronica Rose, ISACA board supervisor and an information systems auditor at Metropol Corp. Ltd., recommends the use of a mix of frameworks to attain the best outcomes. The ISACA Threat IT structure aligns well with the COBIT 2019 structure, Rose stated.
Business Threat Administration Software Application Development: Conveniences & Characteristics, Price. With technological developments, risks are constantly on the surge., organizations navigate with a frequently transforming sea of dangers.
Getting My Risk Management Enterprise To Work
In this blog, we will certainly dive right into the globe of ERM software, exploring what it is, its advantages, features, etc to make sure that you can develop one for your service. Venture Risk Monitoring (ERM) software is the application program for preparation, directing, arranging, and controlling organization tasks and improving danger management processes.With ERM, companies can make informative choices to boost the total durability of the business. Devoted ERM systems are vital for organizations that routinely deal with large quantities of delicate info and multiple stakeholders to approve calculated decisions.
It can be prevented by utilizing the ERM software system. This system automates policy conformity management to keep the company safe and certified.
See This Report on Risk Management Enterprise
You can additionally link existing software application systems to the ERM through APIs or by adding data manually. Businesses can make use of ERM to evaluate threats based on their prospective effect for far better danger monitoring and mitigation.: Including this feature allows customers to get real-time notifications on their devices regarding any kind of threat that might occur and its impact.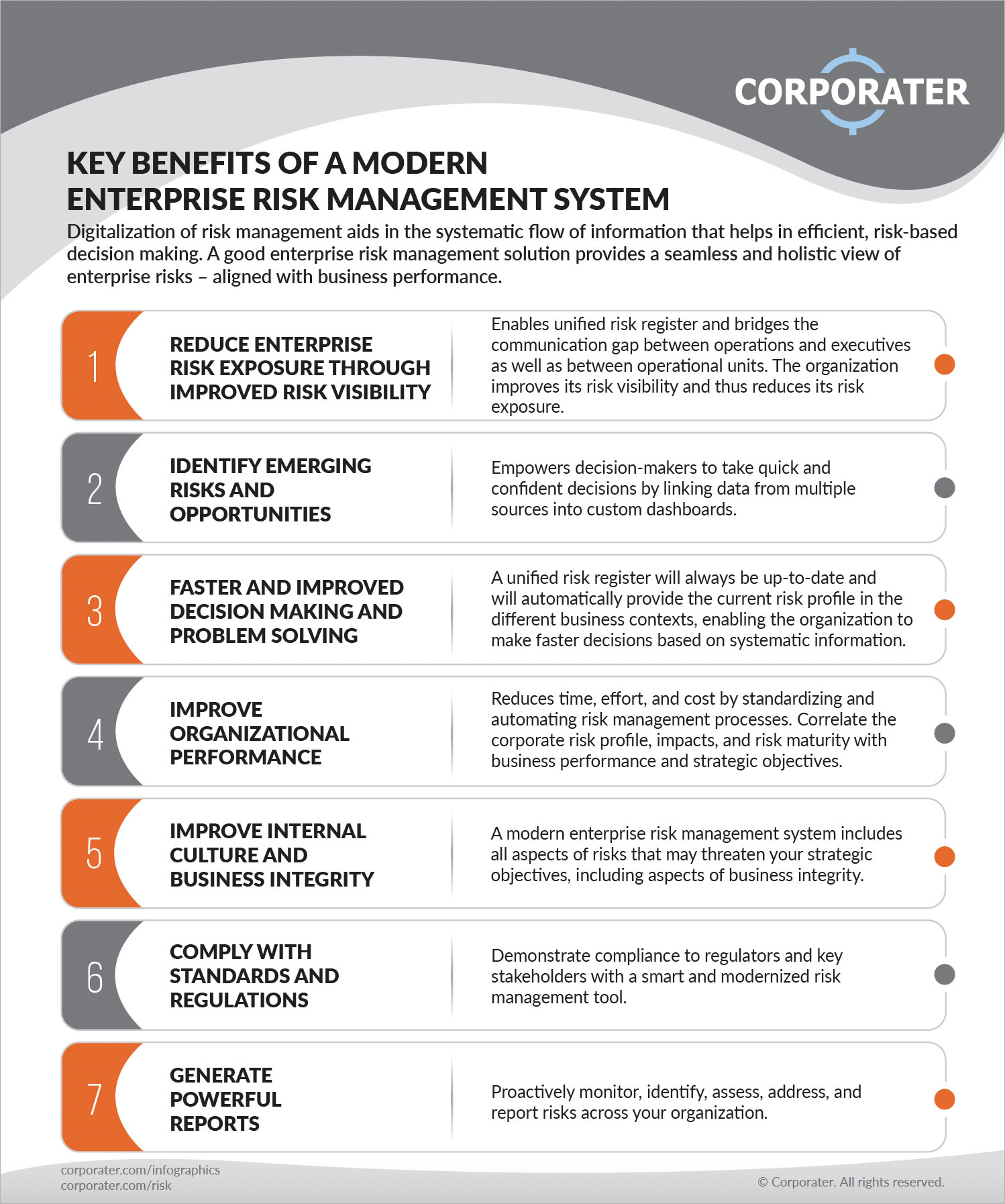
Instead, the software program allows them to establish limits for different procedures and send press notices in case of feasible threats.: By incorporating data visualization and reporting in the Read Full Report customized ERM software program, organizations can get clear understandings regarding risk patterns and performance.: It is compulsory for companies to adhere to industry compliance and regulative standards.
These systems allow companies to apply best-practice risk administration procedures that line up with industry requirements, using an effective, technology-driven approach to recognizing, analyzing, and mitigating threats. This blog checks out the benefits of computerized threat management devices, the areas of threat monitoring they can automate, and the worth they bring to an organization.
Risk Management Enterprise Can Be Fun For Everyone
Teams can establish kinds with the pertinent fields and quickly produce various kinds for various danger types. These risk assessment types can be circulated for completion using automated process that send out alerts to the appropriate team to complete the forms online. If forms are not finished by the deadline, then chaser e-mails are automatically sent by the system.The control surveillance and control testing procedure can likewise be automated. Companies can utilize automated operations to send out normal control test notifications and team can go into the outcomes by means of on-line types. Controls can also be monitored by the software program by setting regulations to send signals based upon control data held in other systems and spreadsheets that is pulled right into the platform by means of API assimilations.
Threat monitoring automation software application can likewise support with danger reporting for all degrees of the business. Leaders can watch reports on threat direct exposure and control effectiveness via a range of reporting outcomes consisting of fixed reports, Power BI interactive records, bowtie analysis, and Monte Carlo simulations. The capacity to draw live records at the touch of a button eliminates difficult information control tasks leaving threat teams with even more time to examine the information and recommend the business on the most click reference effective strategy.
The click to read more need for reliable has actually never been much more pressing. Risk Management Enterprise. Organizations operating in affordable, fast-changing markets can not manage delays or inadequacies in dealing with possible dangers. Traditional risk administration making use of manual spreadsheet-based processes, while acquainted, commonly lead to fragmented data, taxing reporting, and an enhanced probability of human error. Automating the risk administration process with software program addresses these drawbacks.
10 Easy Facts About Risk Management Enterprise Explained
This makes sure risk registers are constantly present and aligned with business goals. Conformity is one more essential motorist for automating risk administration. Specifications like ISO 31000, CPS 230 and COSO all offer assistance around threat monitoring best techniques and control frameworks, and automated risk management devices are structured to align with these requirements aiding companies to meet most generally made use of risk monitoring requirements.Look for threat software program platforms with a consents hierarchy to quickly establish operations for risk escalation. This capability enables you to customize the sight for each user, so they only see the information appropriate to them. Make certain the ERM software program uses user monitoring so you can see that entered what data and when.
Seek out tools that provide task risk management capacities to handle your jobs and portfolios and the associated risks. The advantages of adopting threat monitoring automation software expand far past effectiveness.
The Single Strategy To Use For Risk Management Enterprise
While the situation for automation is compelling, executing a risk monitoring platform is not without its obstacles. For one, data quality is critical. Automated systems count on accurate, current details to supply purposeful insights. To conquer the obstacles of threat management automation, organizations should purchase information cleaning and governance to make sure a solid foundation for executing an automated system.Automation in risk administration empowers businesses to transform their approach to run the risk of and construct a more powerful structure for the future (Risk Management Enterprise). The inquiry is no much longer whether to automate danger monitoring, it's how soon you can start. To see the Riskonnect at work,
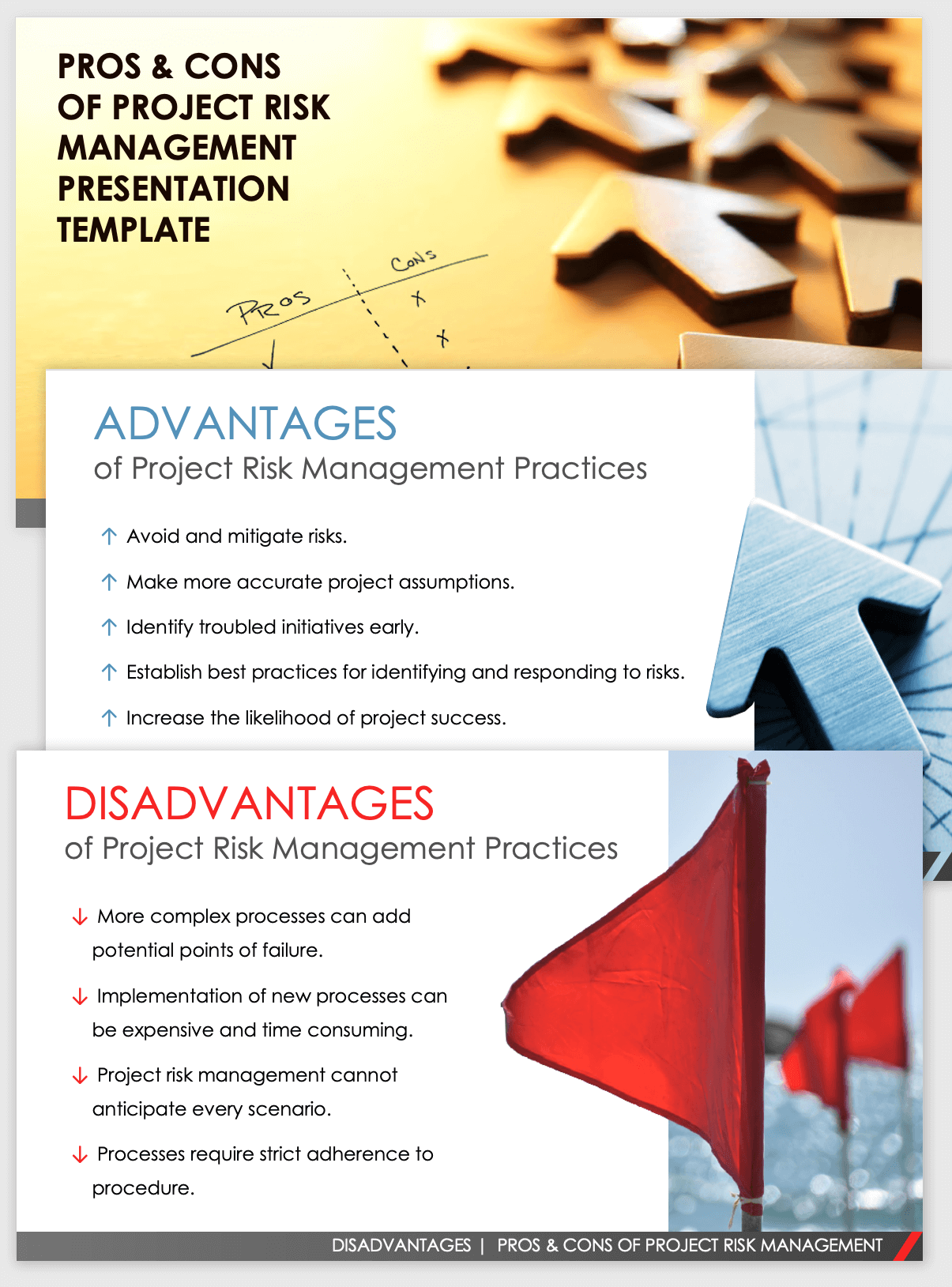
The response frequently lies in how well risks are prepared for and handled. Job monitoring software program serves as the navigator in the tumultuous waters of task implementation, offering tools that determine and evaluate risks and develop techniques to mitigate them effectively.
Report this wiki page